...
All issues from 3.0.0-M0, 3.0.0-M1 and 3.0.0-M2 plus the following.
Bug
- [SYNCOPE-1706] - Notification task not created with event category PROPAGATION
- [SYNCOPE-1707] - Failure when attempting to add Plain Schema via Console
Improvement
- [SYNCOPE-1696] - Audit Elasticsearch persistence
- [SYNCOPE-1708] - Allow enable/disable extensions in enduser
3.0.0-M2 (October 27th, 2022)
...
3.0.0-M0 (August 5th, 2022)
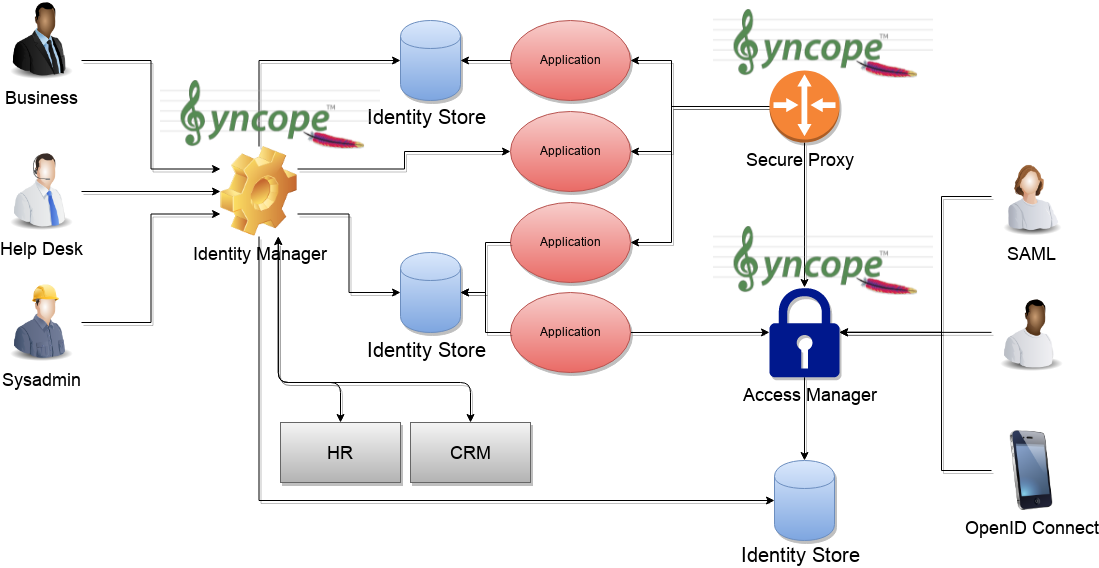
More than 4 years, around 2000 commits after Syncope 2.1 Fusion, here it comes the first release from the new major First milestone release for the new major series Syncope 3.0 Maggiore.Syncope 3.0 Maggiore is now a full-fledged IAM system covering provisioning, reconciliation and reporting needs (as with earlier releases), access management and API management.
What's new
At a general level, all components were (re)written to be based on Spring Boot 2.7 and JDK 11 LTS. JDK 17 LTS is fully supported.
This fact provides the greatest deployment flexibility: each component can be run:
- as web application inside one of supported JavaEE containers
- as standalone application
- as Docker image
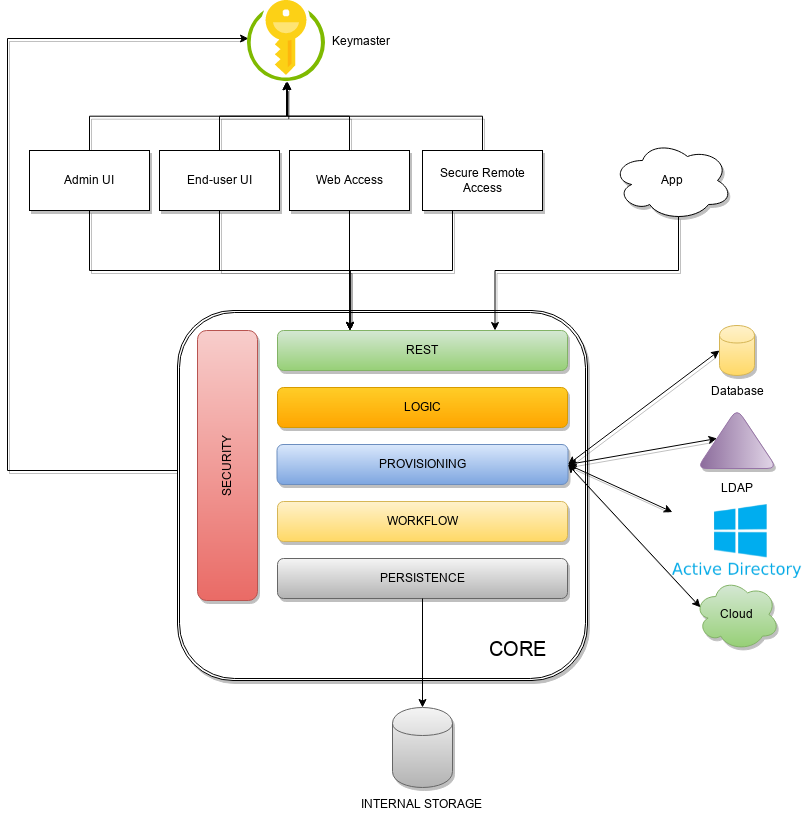
New component: Keymaster
The Keymaster allows for dynamic service discovery so that other components are able to find each other.
On startup, all other component instances will register themselves into Keymaster so that their references can be found later, for intra-component communication.
In addition, the Keymaster is also used as key / value store for configuration parameters and as a directory for defined domains.
Two different implementations are provided, following the actual needs:
- as an additional set of RESTful services exposed by the Core, for traditional deployments (also known as Self Keymaster);
- as a separate container / pod based on Apache Zookeeper, for microservice-oriented deployments.
New component: Web Access (WA)
The Web Access component is based on Apereo CAS: this means (besides the rest) that Authentication, Authorization, Single Sign, OpenID Connect and SAML 2.0 are coming to Syncope.
In addition to all the configuration options and features from Apereo CAS, the Web Access is integrated with Keymaster, Core and Admin UI to offer centralized configuration and management.
New component: Secure Remote Access (SRA)
The Secure Remote Access component is built on Spring Cloud Gateway.
In addition to all the configuration options and features from Spring Cloud Gateway, the Secure Remote Access is integrated with Keymaster, Core and Admin UI to offer centralized configuration and management.
The Secure Remote Access allows to protect legacy applications by integrating with the Web Access or other third-party Access Managers implementing standard protocols as OpenID Connect or SAML.
Revised component: Enduser UI
The End-user UI is the web-based application for self-registration, self-service and password reset.
The communication between End-user UI and Core is exclusively REST-based.
This component was rewritten from scratch in Syncope 3.0, to be technologically aligned with Console UI and based on Apache Wicket.
Migrating from older releases
The distance between earlier releases and Syncope 3.0 Maggiore is relevant under different aspects: architecture, technology, project organization and naturally internal data representation.
For this reason there is no practical way to migrate an old project to Syncope 3.0; it is possible, however, to setup a new Syncope 3.0 project, replicate configurations and finally migrate the existing data.
Here is the outlined approach:
...
Issues
Sub-task
- [SYNCOPE-1413] - Remove CLI
- [SYNCOPE-1414] - Remove GUI Installer
- [SYNCOPE-1418] - Convert webapps to Spring Boot
- [SYNCOPE-1421] - New Enduser UI
- [SYNCOPE-1426] - Remove Eclipse IDE plugin
- [SYNCOPE-1458] - Keymaster for Configuration Parameters
- [SYNCOPE-1459] - Keymaster for Service Discovery
- [SYNCOPE-1460] - Keymaster for dynamic Domain management
- [SYNCOPE-1494] - Basic maven build to verify compilation correctness
- [SYNCOPE-1495] - Remove deb packages
- [SYNCOPE-1496] - Add integration tests for DBMSes via Docker
- [SYNCOPE-1552] - Allow WA audits to be stored in Syncope
- [SYNCOPE-1553] - Fetch WA auth modules & map to properties during bootstrap
- [SYNCOPE-1555] - Allow WA as SAML2 IdP to fetch metadata over REST
- [SYNCOPE-1556] - Allow WA as OIDC OP to fetch JWKS over REST
- [SYNCOPE-1557] - Complete policies manipulating with authentication modules and mappings information
- [SYNCOPE-1558] - Configure WA delegated authn module to SAML IdPs via REST
- [SYNCOPE-1559] - Allow WA Google Auth MFA settings to become reloadable
- [SYNCOPE-1562] - Handle OTP records for GoogleAuthN MFA
- [SYNCOPE-1566] - Manage device registration records for GoogleAuthMFA
- [SYNCOPE-1570] - Support U2F device registration via REST APIs
- [SYNCOPE-1571] - Support U2F MFA tokens/requests via REST APIs
- [SYNCOPE-1577] - Support CAS-enabled client applications
- [SYNCOPE-1578] - Protected SRA Routes: OAuth 2.0 / OpenID Connect 1.0
- [SYNCOPE-1579] - Protected SRA Routes: SAML 2.0
- [SYNCOPE-1580] - Design WA REST APIs to configure configuration properties
- [SYNCOPE-1582] - Protected SRA Routes: CAS
- [SYNCOPE-1584] - Allow Syncope to manage WA authentication events
- [SYNCOPE-1587] - Enable Web AuthN support for WA
- [SYNCOPE-1588] - WA attributes consent management
- [SYNCOPE-1595] - Support themes per client application
- [SYNCOPE-1599] - Support Duo Security for MFA
- [SYNCOPE-1625] - Support impersonation for Web Access
- [SYNCOPE-1638] - Remove Netbeans IDE plugin
- [SYNCOPE-1682] - WA: support CAS Attribute Resolution
...